A password manager is a software application or a hardware device used to store and manage a person’s passwords and strong passwords. Typically all stored passwords are encrypted, requiring the user to create a master password to access all the stored, managed passwords.
In this definition...
Common features of password managers
Password managers share a few features:
- A master password gives you access to your password manager vault. It’s the one password you must remember.
- Vaults store items (usernames, passwords, and files) securely. In enterprise settings, organizations will establish shared vaults to store passwords that multiple users need.
- Collaboration and sharing: Many password managers allow collaboration with other users through the application, to facilitate safely sharing passwords or vaults.
Top password management vendors
1. 1Password 

1Password is a password management system employed by enterprises to store employee passwords. 1Password allows users to save complex, strong passwords without memorizing them. 1Password uses AES 256-bit encryption to protect passwords. Passwords created are encrypted and hosted on AgileBit’s secure servers.
With 1Password, individual users and IT staffs can create Vaults for specific sets of passwords. If they want to safely share a password with other team members, that employee can be added to the Vault. They’ll gain the ability to use the login credentials without having visibility of the password itself. Along with browser extensions and freestanding applications for macOS, iOS, Windows, Android, Linux, ChromeOS, and command line, 1Password is can be downloaded as a mobile app on iOS and Android phones.
In addition to individual, family, and tiered ed enterprise plans, 1Password offers a two-week free trial.
 Available in both individual and business configurations, RoboForm allows users to store their encrypted credentials and other sensitive data either locally or in the cloud. RoboForm launched in 1999, making it one of the oldest password management systems in operation. Secure sharing of logins, as well as credit card storage, safe notes, bookmarks, contacts, application passwords, and online form fills, are all part of the standard feature set, as well as a random password generator capable of generating passwords up to 512 characters long.
Available in both individual and business configurations, RoboForm allows users to store their encrypted credentials and other sensitive data either locally or in the cloud. RoboForm launched in 1999, making it one of the oldest password management systems in operation. Secure sharing of logins, as well as credit card storage, safe notes, bookmarks, contacts, application passwords, and online form fills, are all part of the standard feature set, as well as a random password generator capable of generating passwords up to 512 characters long.
RoboForm’s enterprise tier uses AES256 bit encryption to protect the creation, storage, and use of compliant passwords. IT teams can set policies, delegate permissions, manage users, and report on usage
2. Dashlane 
Dashlane is a password management tool that can perform both basic and advanced tasks depending on your needs. It creates, saves, and autofills strong, randomized passwords for all accounts, so you’ll never have to remember or worry about your passwords. Dashlane is designed so that they can’t see the information users store in it, meaning your data will never be sold. A VPN is included to scan your account for weak and compromised passwords. A free version of Dashlane is available, and plans that are priced annually are available for individuals, families, and businesses.
is a password management tool that can perform both basic and advanced tasks depending on your needs. It creates, saves, and autofills strong, randomized passwords for all accounts, so you’ll never have to remember or worry about your passwords. Dashlane is designed so that they can’t see the information users store in it, meaning your data will never be sold. A VPN is included to scan your account for weak and compromised passwords. A free version of Dashlane is available, and plans that are priced annually are available for individuals, families, and businesses.
3. NordPass 
 NordPass allows you to store all your passwords in a single place and log in to your most-used websites and apps with a single click. Even when you’re offline, your login credentials can still be accessed. Passwords can be shared with people you trust through an encrypted vault. NordPass syncs all passwords across all devices, and there is no limit on the amount of passwords you can store. It comes with a built-in password generator, and sensitive notes and credit card information can also be stored. The application has a free version in addition to premium and family premium versions.
NordPass allows you to store all your passwords in a single place and log in to your most-used websites and apps with a single click. Even when you’re offline, your login credentials can still be accessed. Passwords can be shared with people you trust through an encrypted vault. NordPass syncs all passwords across all devices, and there is no limit on the amount of passwords you can store. It comes with a built-in password generator, and sensitive notes and credit card information can also be stored. The application has a free version in addition to premium and family premium versions.
How to use a password manager
Today, people have a large number of passwords for social media sites, work logins, shopping pages, online banking, and much more. While it is important to use strong passwords and to use different passwords on each site, it can be a difficult task to remember all of them. With a password manager, you simply enter the site, provide the master password you set for the password manager in that software, then log in to the site and the username and password will be stored for you.
Using a password manager can also help you to create more secure passwords as it will create randomly generated passwords if you create new online accounts using the manager. Often, with a master password you can sync accounts across platforms as well.
Managing passwords in a web browser
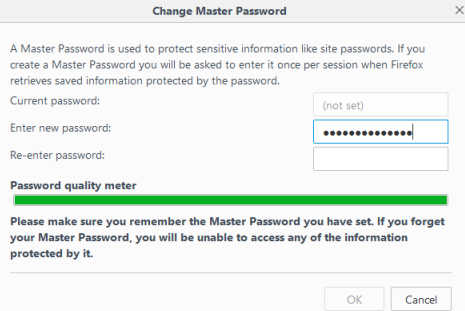
Most web browsers —Chrome, Firefox, and Explorer—have an integrated password manager, but they do not encrypt the passwords, so anyone with access to your computer can view your online passwords quite easily. Some options exist, like on Firefox, to encrypt passwords and use a master password to retrieve. While this makes the password manager more secure, browser-saved passwords typically will not work across platforms and the password managers lack features, including the ability to generate random passwords for new accounts.
Are built-in password managers secure?
Built-in password managers, such as Keychain in macOS, have automatic strong-password-generation features and security features. According to Apple, keychain metadata is encrypted, and keychain items use 256-bit AES encryption. The downside to a built-in password manager is that you don’t have to log in every time you want to use it. There is no master password. If someone hacks your physical computer and wants to access an account, and you’re using 1Password, they’ll have to know the master password before they can access that account. If you’re using a built-in app like Keychain, your login information will automatically show in the fields.
Built-in password managers present a risk if you’re commonly working around other people and leave your computer open for spans of time or if you work in a location with people who aren’t part of your organization. They are less risky for personal computer users, especially if you’re only using your laptop at home. It’s also safer to use built-in password managers only for accounts that have less sensitive data (for example, using Keychain for a My Panera account but not for your bank account).
Hardware password managers
Many hardware-based password manager devices work in a similar fashion to software password managers. You first install an app on your PC and connect the password manager using a USB port on the computer. When login pages are detected users are prompted to save the logins to the password device. All usernames, password and other required login information is stored encrypted, often on a protected smart card.
The app for the device can be customized to manage logins, information and to import or export credentials from various locations, including cloud storage.
Why should businesses use password managers?
Businesses use password managers to store strong passwords so that employees don’t have to memorize them or write them down in places where they could be stolen. Password management software also eliminates the need to share plaintext passwords with coworkers by leaving a note on their desks or sending them an email with the password.
Too, password managers largely eliminate the need to share login credentials for business platforms and enterprise applications across internal communications channels.
With companies relying on cloud-based platforms for business-critical systems like customer relationship management, enterprise resource planning, finance, logistics, product lifecycle management, shared cloud storage, wireless networks, VPNs, productivity suites, and many more, an enterprise-wide password management system reduces the password fatigue that arises from needing to remember multiple passwords.
For example, if several employees are responsible for updating their company’s social media presence, IT may make the decision to issue a single set of credentials for the employees to share. In a situation like this, those employees might need to send the shared username and password through email, over chat channels, or even pass a sticky note from cube to cube.
Password managers not only collect these credentials in a secure environment, but also allow IPSec teams to easily control access for new employees, revoke access for employees who have left, and even enforce password complexity and aging standards.
The stakes for keeping passwords safe across the enterprise as a comprehensive data security strategy have never been higher. In a 2021 study by Infosys, researchers estimated that the world’s top 100 most valuable brands stood to lose value totalling between $93 billion and US$223 billion were a breach to compromise their mission-critical systems.

