DMZ
A demilitarized zone, or DMZ, in computing is a subnetwork between a local network and external networks like the internet to protect internal users and data from threats to the network perimeter.

The global wide-area network (WAN) known as the internet is an open ecosystem offering content, products, and threats to organizations. For businesses or organizations protecting sensitive client information or proprietary secrets, the internet is one of the most severe threat vectors to data. Online threat actors are persistent, and having a DMZ adds a foundational layer of cybersecurity for managing external and internal network user activity and access.
While DMZ frameworks are less pertinent thanks to cloud storage, the buffer zone remains essential for on-premises security and complementing newer strategies like zero trust network access (ZTNA).
This article describes a demilitarized zone in IT networking, how it works, the benefits of perimeter networks, and trends.
In this definition...
What is a Demilitarized Zone (DMZ)?
A demilitarized zone (DMZ) is an IT security framework for protecting trusted local-area networks (LAN) by passing all untrusted external traffic through an intermediate proxy network.
DMZ networks are also known as perimeter networks. They sit between a physical location’s internal network (also known as a local-area network or LAN) and the public internet where web-based threats loom.
Also read: Client-Server Model | A Guide to Client-Server Architecture | ServerWatch
How Do DMZ Networks Work?
Demilitarized zone networks often contain systems enabling network administrators to manage internet traffic, file transfers, email, and access management. This infrastructure can be physical appliances, software-based, or virtual to create buffer zones for complex architectures.
Organizations can create a DMZ that establishes an additional network segment controlled by IT administrators with a single or dual-firewall approach and proper routing. Network operators can monitor and set policies for internal and external parties, isolate and block specific threats, and ensure continued access to authorized users and devices.
Architecture: Single vs. Dual Firewalls
In the early days of DMZ implementation, organizations could use a single firewall to filter traffic entering the local network from the internet or vice-versa and exiting traffic leaving the internal network. Naturally, adding a second firewall on the opposite side of the DMZ network came next and is now the most common and implemented approach. With firewalls evaluating traffic from both ends, administrators have the most visibility and control into protecting the internal network.
Read more: Top Next-Generation Firewall (NGFW) Vendors for 2021 | eSecurityPlanet
Public-Facing Servers
DMZ networks contain public-facing servers responsible for establishing ongoing and secure communication between internal and external parties. Devices accessible to internet traffic include web servers (HTTP/S), FTP servers, mail servers (SMTP), VoIP servers, and DNS servers to connect network users in an administrator-controlled environment. With control over data accessible within the perimeter network, organizations can protect more sensitive data within the network core.
Benefits of a DMZ Network
- Network segmentation offers increased visibility, control, and security
- Identity access management and control of specific public internet content
- Scan and block malicious IP addresses and IP spoofing
- Facilitate web, mail, proxy, FTP, and DNS server workloads in secured zone
- Prevent advanced persistent threats and internal network reconnaissance
The Decline of the DMZ Network
DMZ networks are a valuable security apparatus for protecting sensitive, on-premises data. Still, the rise of cloud computing means small businesses up to enterprise organizations don’t possess as much local data. For sensitive data and critical workloads, a DMZ remains an essential security layer for preventing escalating threats.
As organizations increasingly consider insider threats and lateral movement rather than securing the network perimeter, zero trust becomes a top security consideration. DMZ networks and zero trust strategies both address access and prevent exploits. The difference is demilitarized networks fixate on stopping initial access to the internal network. Zero trust assumes initial access and creates additional security around specific inner network segments, also known as microsegmentation.
Also read: Zero Trust Security Architecture Overview | Developer.com
Origin of DMZ as a Term
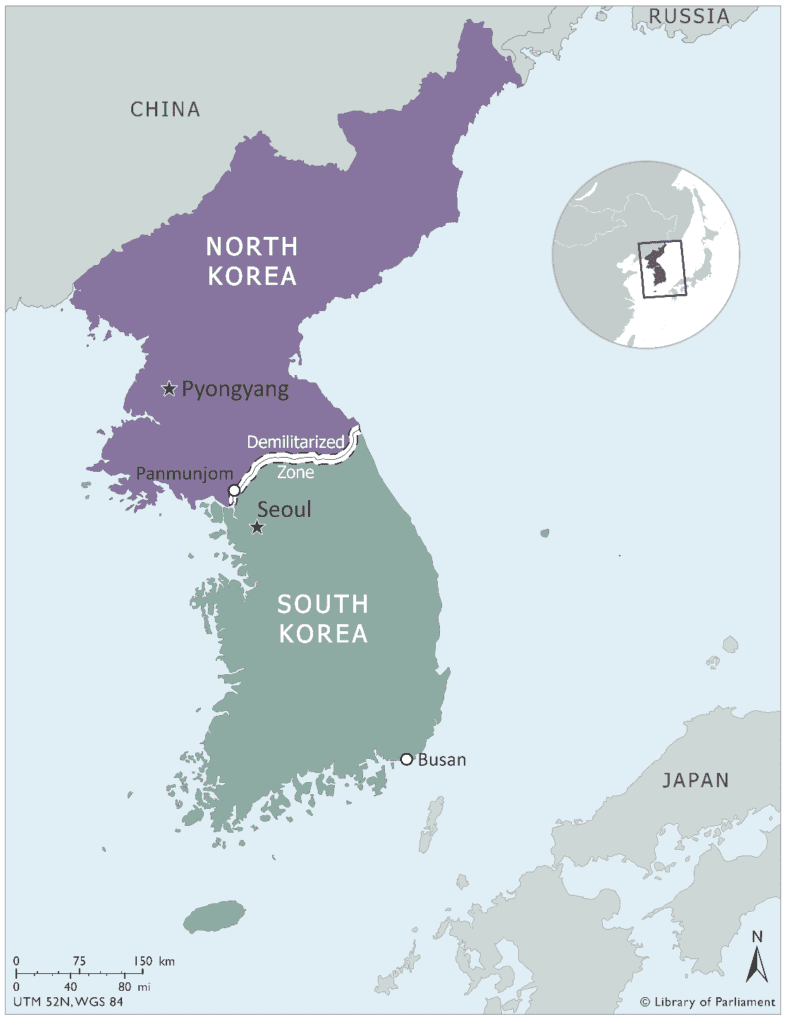
Demilitarized zones have long been the geographic regions where two nations forbid military activity through a diplomatic arrangement. The most notable of which is the Korean DMZ separating North and South Korea since 1953. Demilitarized zones are types of buffer zones like neutral grounds and border zones for any two nations.
The purpose of buffer zones is often to deter or impede migration across the zone. Similarly, DMZ networks in computing work to allow and block specific users and traffic from breaching the trusted internal network.
Recent Coverage
- DMZ vs Zero Trust | Is DMZ Network Dead? | ServerWatch
- Database Security: 7 Best Practices & Tips | eSecurityPlanet
- 5 Shortcomings of Legacy Firewalls for Internal Data Center Security | eWEEK
- Steps to Improving Your Data Architecture | IT Business Edge

