A kill chain is used to describe the various stages of a cyber attack as it pertains to network security. The actual model, the Cyber Kill Chain framework, was developed by Lockheed Martin and is used for identification and prevention of cyber intrusions.
The actual steps in a kill chain trace the typical stages of a cyber attack from early reconnaissance to completion where the intruder achieves the cyber intrusion. Analysts use the chain to detect and prevent advanced persistent threats (APT).
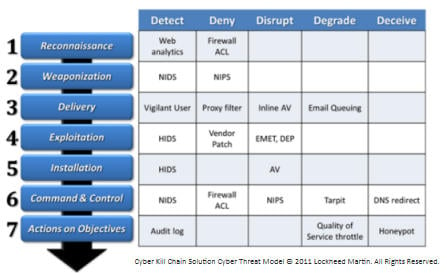
The 7 steps of The Cyber Kill Chain
According to Lockheed Martin’s APT documentation, the seven steps of the Cyber Kill Chain include the following:
- Reconnaissance – Example: harvest email accounts
- Weaponization – Example: couple an exploit with a backdoor
- Delivery – Example: deliver bundle via email or Web
- Exploitation – Example: exploit a vulnerability to execute code
- Installation – Example: Install malware on target
- Command and Control – Example: Command channel for remote manipulation
- Actions on Objectives – Example: Access for intruder to accomplish goal
Image Source: Seven Ways to Apply the Cyber Kill Chain; Lockheed Martin Corporation.
Cyber Kill Chain is a registered trademark of Lockheed Martin Corporation.