The third technical preview of Windows Server 2016 introduced Windows Server Containers capabilities (later referred to simply as Windows Containers), which provide operating system-level virtualization that allows for multiple isolated applications to be run on a single system.
Windows Containers provide application isolation through process and namespace isolation technology by sharing a kernel with the container host and all other containers running on the host.
Windows Containers vs. Hyper-V Containers
Windows Server 2016 actually offers two different types of container runtimes, each with different degrees of application isolation. Windows Containers offer isolation through namespace and process isolation, whereas Hyper-V Containers isolate each container via a lightweight virtual machine (VM).
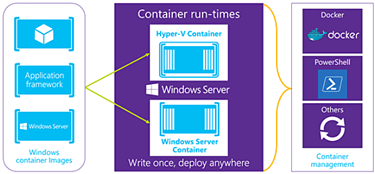
Windows Containers share a kernel with the container host and all the containers running on the host. In contrast, with Hyper-V Containers the kernel of the container host is not shared with the Hyper-V Containers.
What this means is that Windows Containers are isolated from each other but they run directly on Windows Server 2016. Hyper-V Containers on the other hand provide enhanced isolation by running the containers from a Hyper-V VM.
Both Windows Containers and Hyper-V Containers can be managed using either Windows PowerShell or Docker. In the case of Docker, containers can be managed from the Docker CLI (command-line interface) using the same commands currently used to create and run Docker containers on Linux.

