Biometric fingerprint readers, or scanners, are the most popular and most common form of biometric security devices used.
Biometrics consists of automated methods of recognizing a person based on unique physical characteristic. Each type of biometric system, while different in application, contains at least one similarity: the biometric must be based upon a distinguishable human attribute such as a person’s fingerprint, iris, voice pattern or even facial pattern.
Today fingerprint devices are by far the most popular form of biometric security used, with a variety of systems on the market intended for general and mass market usage. Long gone are the huge bulky fingerprint scanners; now a fingerprint scanning device can be small enough to be incorporated into a laptop for security.
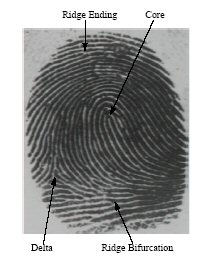
Image Source: MSU Biometrics (2004)
A fingerprint is made up of a pattern of ridges and furrows as well as characteristics that occur at Minutiae points (ridge bifurcation or a ridge ending).
Fingerprint scanning essentially provides an identification of a person based on the acquisition and recognition of those unique patterns and ridges in a fingerprint.
The actual fingerprint identification process will change slightly between products and systems. The basis of identification, however, is nearly the same. Standard systems are comprised of a sensor for scanning a fingerprint and a processor which stores the fingerprint database and software which compares and matches the fingerprint to the predefined database. Within the database, a fingerprint is usually matched to a reference number, or PIN number which is then matched to a person’s name or account. In instances of security the match is generally used to allow or disallow access, but today this can also be used for something as simple as a time clock or payroll access.
In large government organizations and corporations, biometrics plays a huge role in employee identification and security. Additionally some data centers have jumped on the bandwagon and have implemented biometric scanners to enhances remote access and management by adding another layer of network security for system administrators. Unfortunately the cost of implementing fingerprint and other biometric security scanning in data centers is still quite expensive, and many centers still rely on ID badges while waiting until biometric technology becomes a little more pocket-book friendly.
Today companies have realized that fingerprint scanning is an effective means of security. While the cost of implementing biometric scanners in larger organizations and data centers is still quite costly, we did find several fingerprint scanning devices which would fit into the budget of many small offices and home users. These home and small office products are designed to protect your hard drive, notebook or even to remove the need for users to remember multiple passwords.
Recommended Reading: How Biometrics Security Works
Based in Nova Scotia, Vangie Beal is has been writing about technology for more than a decade. She is a frequent contributor to EcommerceGuide and managing editor at Webopedia. You can tweet her online @AuroraGG.
This article was originally published on October 01, 2004

